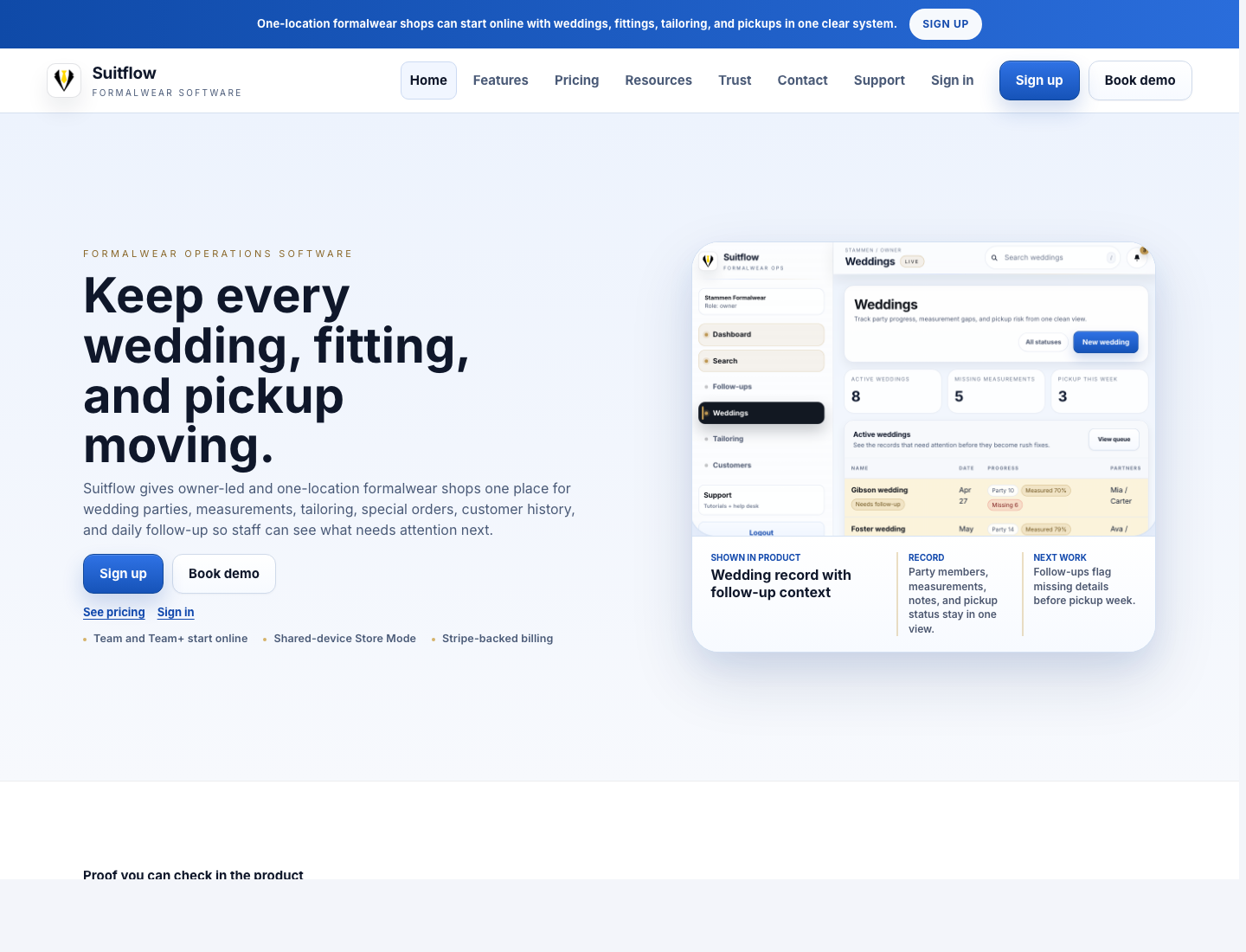
SuitFlow
Formalwear operations software for weddings, measurements, tailoring, special orders, customers, follow-ups, messaging, staff access, and billing.
These projects show different sides of the same builder profile: B2B SaaS, privacy-first consumer software, applied AI, infrastructure, cybersecurity, automation, and founder-led delivery.
The public case studies include real screenshots where available. Atlas intentionally uses placeholders until Caleb provides real app screenshots.
Formalwear operations software for weddings, measurements, tailoring, special orders, customers, follow-ups, messaging, staff access, and billing.
Local-first SwiftUI and SwiftData travel map for privately tracking places visited, trips, goals, heatmaps, widgets, shareable cards, and exports.
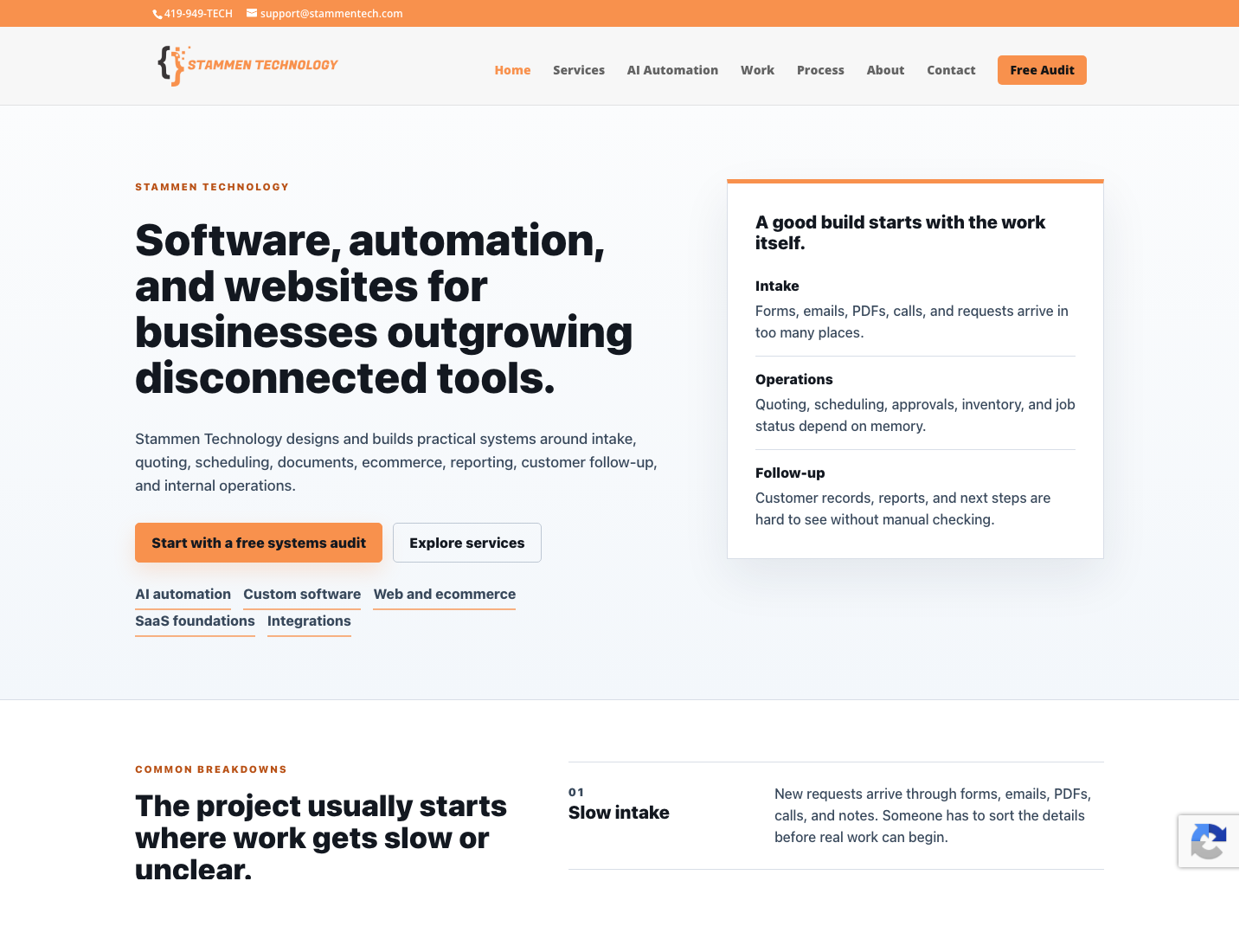
Custom software, AI, web development, ecommerce, mobile applications, automation, and SaaS foundations for businesses outgrowing disconnected tools.
Some of the strongest work is internal. These summaries avoid employer-sensitive details while showing the type of problem, technical approach, and operational value.
Internal AI systems supporting architecture workflows, including meeting minutes, onboarding, communications, project information routing, intranet, learning, and knowledge workflows.
Infrastructure, cybersecurity, industrial networking, recovery planning, vendor coordination, and a custom C# automation that current resume material reports saved 200+ labor hours annually.
B.S. capstone work simulated an enterprise network under attack, demonstrated how to stop the attack, identified security weaknesses, and included disaster recovery and business continuity planning.
Graduate work at WGU covered secure network design, security operations, secure software design, cloud security, penetration testing, cybersecurity architecture, governance, risk, and management.
AI, software, infrastructure, cybersecurity, and product work all point to the same thing: I like systems that solve real problems and can be trusted after launch.